A Tale of Two Markets: Investigating the Ransomware Payments Economy | August 2023 | Communications of the ACM

A Tale of Two Markets: Investigating the Ransomware Payments Economy | August 2023 | Communications of the ACM
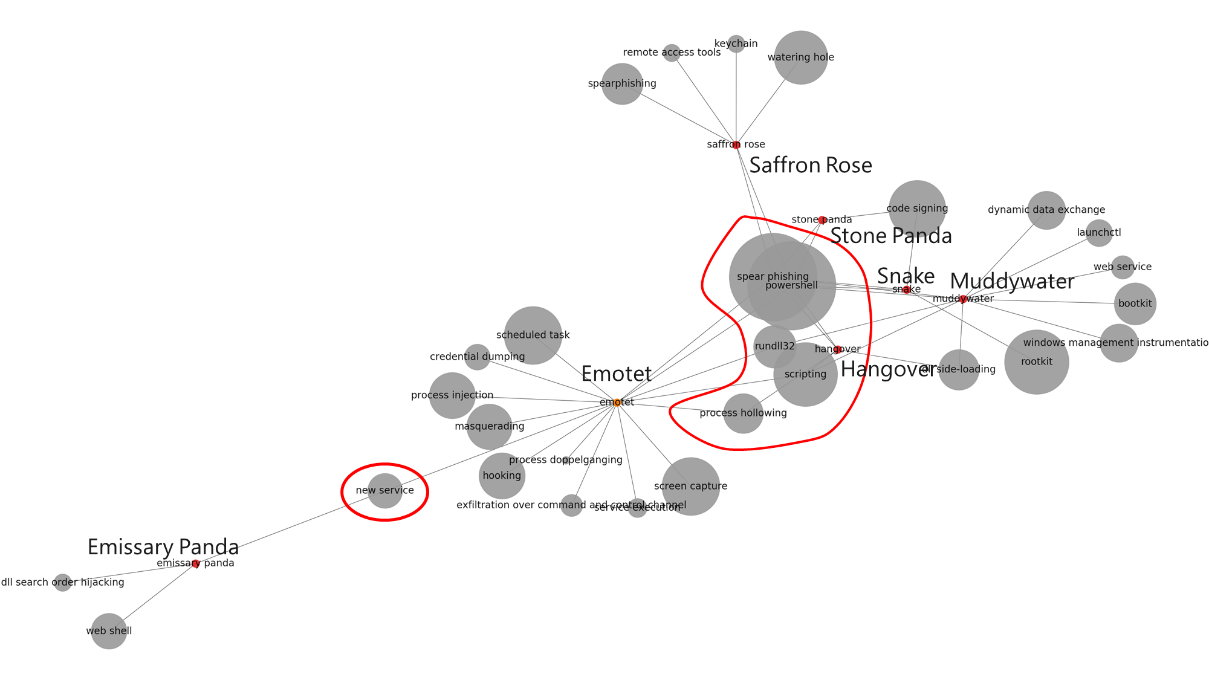
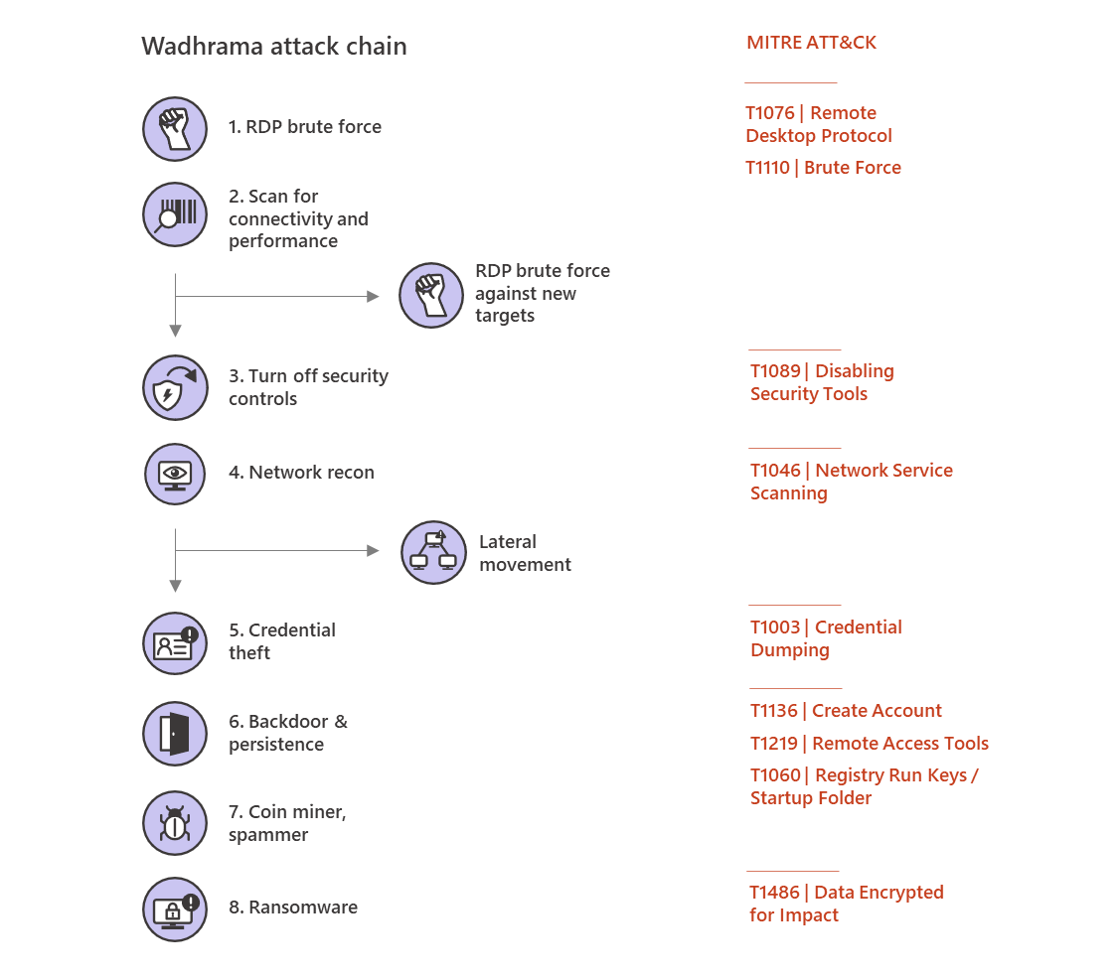
What's your major threat? On the differences between the network behavior of targeted and commodity malware

The distribution of targeted and commodity malware with respect to the... | Download Scientific Diagram

A Tale of Two Markets: Investigating the Ransomware Payments Economy | August 2023 | Communications of the ACM